Related Posts

How Smaller Firms Can Achieve Data Lineage with Simple Agents
Data lineage isn't about expensive technology. It's about answering three straightforward questions... read more
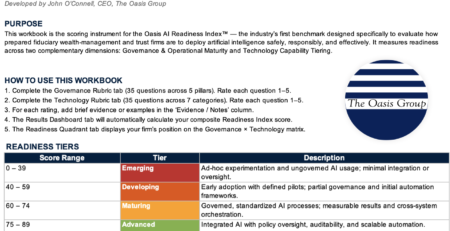
The Oasis Group’s AI Readiness Index: First Maturity Benchmark for Wealth Management Industry
The Oasis AI Readiness Index™ is the industry’s first maturity benchmark... read more
Where Does AI Fit in Your Firm’s Future?
This article provides a brief guide to the AI technologies available today,... read more

Using Claude to Create a Monte Carlo Retirement Simulation
Monte Carlo simulations have become an invaluable tool for financial advisors and... read more

Navigating the Digital Minefield: A Guide for Financial Advisors on TikTok and Temu
In an era where digital convenience intersects with unparalleled risks, financial advisors... read more

The Talent Crisis vs. The Millionaire Boom: How AI Will Decide Which Wealth Firms Survive
The wealth management industry is headed for a collision between unprecedented demand... read more

How Wealth Management Firms Should Engage With the Rise of Prediction Markets
In our latest Peaks Perspective article, we delve into the rise of... read more

The Strategic Imperative of Appointing a Chief Growth Officer
In the dynamic landscape of wealth management, the quest for sustainable growth... read more

Your Wealth Management CRM Doesn’t Have Sales Stages – And It’s Costing You Clients
Your conversion process has stages whether your CRM acknowledges them or not.... read more

From AI Assistants to AI Employees: How Agentic Workforces Are Reshaping Wealth Management Operations
In this Peaks Perspective article, Nathaniel Hettrick of The Oasis Group discusses... read more

