Ransomware Group BlackCat/ALPHV Weaponizes SEC Disclosure Rules
The digital era has brought with it an increase in cyber threats that target businesses of all sizes. As a response to this growing problem, the SEC introduced new regulations that compel companies to publicly disclose their breaches within specific deadlines. However, the recent complaint filed with the SEC by the ransomware group ALPHV (aka “BlackCat”) highlights the challenges that businesses face in complying with these regulations. This article explores the implications of ALPHV’s complaint and how it could impact businesses.
Ransomware Groups Grew in Sophistication
Traditional ransomware attacks are where a bad actor infiltrates a target company’s computer systems, copies sensitive information, and encrypts that information on the target company’s computer systems. This encryption renders the information unreadable by the target company without an encryption key. Ransomware attacks emerged in the mid to late 2000s and started with bad actors extorting a ransom from the target company for the encryption keys to unlock the data. This type of attack became prevalent between 2013 and 2016.
Ransomware groups continued to grow in sophistication and scope. The landscape of ransomware attacks continued to evolve, with bad actors adopting increasingly refined approaches. A notable shift is the implementation of a sliding scale for ransom payments, whereby the ransom amount escalates the longer a business takes to pay.
Bad actors implemented new blackmail tactics with the rise of leak sites in early 2019. This attack includes a traditional ransomware attack with the threat of blackmail. The bad actor threatens to leak the target company’s sensitive information on the bad actor’s public website. This can be incredibly damaging to the company and its senior executives. Bad actors have published compensation tables, executive personal records and addresses, and other sensitive company information on their websites when they are not paid.
In an innovative twist, some threat actors began to bypass the often-costly process of encrypting data altogether. Instead, they copy the target company’s sensitive information and threaten to leak it online or sell the information on the dark web. The MOVEit cybersecurity incident from 2023 was an example of an incident where the bad actor did not encrypt the target company’s data and simply threatened to publish and sell the sensitive information (see VantagePoint Vol 1 Issue 6 for more on this attack). The bad actor from the MOVEit incident did publish hundreds of gigabytes of sensitive data publicly. This extortion by blackmail tactic can be particularly effective depending on the nature of the target’s business and its data.
Setting the Stage for the Latest Tactic.
The SEC passed new regulations to provide a consistent method for public companies to disclose cybersecurity issues. SEC Chair Gary Gensler remarked, “Whether a company loses a factory in a fire — or millions of files in a cybersecurity incident — it may be material to investors. Currently, many public companies provide cybersecurity disclosure to investors. I think companies and investors alike, however, would benefit if this disclosure were made in a more consistent, comparable, and decision-useful way.”
The SEC’s new regulations aim to enhance transparency and promote timely reporting of cyber incidents that may impact the financial market. Businesses must identify breaches that pose material risks to their operations and notify their clients, shareholders, and regulators within specific timeframes. However, the complexity of modern cyber threats and the sophistication of cybercriminals mean that compliance can be challenging for businesses. They often find it difficult to determine whether a breach is material, how long it takes to investigate it fully, and the precise impact of the breach.
The new disclosure rules became effective on September 5, 2023, and the incident reporting requirements were implemented on December 15 for larger publicly traded companies. Smaller firms have a 180-day grace period after the December 18th deadline to commence incident reporting. These new rules set the stage for a new extortion tactic for bad actors: threatening to file a formal complaint with the SEC if the target company does not pay the ransom.
A New Tactic to Extort Ransoms
An attack in November highlights the concerns for SEC regulated firms. ALPHV, a prolific ransomware group, successfully attacked MeridianLink, a digital lending service provider, and exfiltrated its files without encrypting them. The ransomware group had a single interaction with MeridianLink, and, after that single interaction, they failed to engage the company in negotiations over the stolen data.
The group then posted the data on its leak site and tried an unprecedented extortion tactic by filing a report about its own crime to the SEC. ALPHV accused its victim of failing to comply with new SEC regulations that require companies to publicly disclose their breaches within certain deadlines.
The ransomware group ALPHV’s formal complaint to the SEC highlights the challenges that businesses face in complying with new regulations on disclosing cyber incidents. This raises questions about how businesses can effectively comply with these regulations while dealing with cyber threats. Some businesses may feel pressure to meet the SEC deadline without thoroughly investigating the incident. Reporting the incident too soon can have serious implications including:
- Incomplete or inaccurate reports of the extent of the incident,
- An incomplete understanding of the extent of the breach, or worse
- Enable other bad actors to capitalize on the same vulnerability
Ransomware groups like ALPHV can exploit the regulations’ deadlines by leaking stolen data before the company has fully investigated the incident and disclosed it to the SEC. This creates a double jeopardy situation for the public company. Failure to comply with SEC regulations may result in reputational damage and legal liabilities. However, completing a thorough investigation may result in the publication of sensitive data by the ransomware group which also may result in reputational damage and legal liabilities.
ALPHV’s weaponization of the SEC disclosure rules has far reaching implications beyond public companies and to wealth management firms. Failure to understand the extent of the cybersecurity incident may result in the bad actor posting the target company’s information on their website and cause significant reputational and financial damage. Bad actors can file a formal complaint on any wealth management firm regulated by the SEC or FINRA related to a cybersecurity incident. Therefore, the jeopardy is not limited to publicly traded companies.
The MeridianLink incident underscores the importance of adopting robust cybersecurity practices and working closely with cybersecurity experts to develop effective incident response plans. A strong incident response plan can enable your business to quickly determine the extent of a cybersecurity incident and your disclosure requirements. Your firm should consider developing an incident response plan or working with cybersecurity experts to develop one. It could be one of your best investments in 2024.
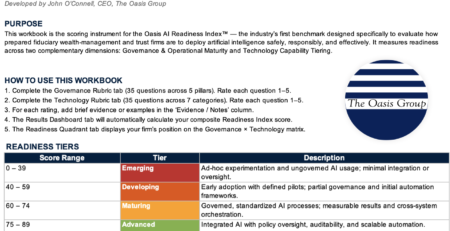
Subscribe to The Vantage Point Newsletter
Join our newsletter to get topics like this delivered straight to your inbox every month!